In May of 2018 i reported this issue to Cloudflare through HackerOne. Domains that have been pointed to Cloudflare by their respective owners through their registrar that have been removed from Cloudflare, can be hi-jacked by other Cloudflare users.
Title: Hi-jacking cloudflare domains due to removal
Weakness: Improper Access Control - Generic
Severity: Medium (5.3)
Link: <Redacted>
Date: 2018-05-16 18:57:57 +0000
By: hackerone.com/@ravun
REPRODUCTION
You can reproduce the root cause of the problems that will be described using the following steps:
- Delete a previously configured domain in your cloudflare account that is still pointed to the cloudflare dns servers such as cody, kirk or coco
- Create a new Cloudflare account that is not in any way associated with your previous account.
- Register the domain you just removed from the other account to your new account which should automatically succeed due to the dns still being pointed to Cloudflare.
SUMMARY
What I see as the root of the issue here is lack of validation on domains that are added to Cloudflare during the setup process. The act of simply pointing your name servers to Cloudflare does not appear to be enough to validate that, the user running setup is the user that owns the domain
PROBLEM
Domains that have been pointed to Cloudflare by their respective owners through their registrar that have been removed from Cloudflare, can be hi-jacked by other Cloudflare users. This can be used to control certificates and content hosted in the image of the domain owner. Furthermore, victims of this will find it very difficult to re-add their domain back to Cloudflare without the other user first removing it.
VIABILITY
Initially, when I found that this was possible I did not see a direct method for viable exploitation unless you both already knew the domain name you wanted to hi-jack, and when it was removed from Cloudflare - which at that time meant it was not worth reporting.
However, a few weeks ago, I had a dangling honey pot domain that i had removed but was still pointed. Sure enough the domain was hi-jacked by what seemed to be a Russian bot net. The domain was then pointed to appeared to be a gambling site for bitcoin (in Russian). My domain was fairly unknown and never marketed, or indexed. Speculation as to how the domain was targeted aside, it's clear that this exploit is being used in the wild.
SPECULATION
Please ignore this section if you do not care about my speculation. However, I have been trying to figure out how my domain could have been targeted. The only two methods I could come up with are:
- A scanner seeking all known Cloudflare hosted sites using known Cloudflare ips and adding them to a list.
- Monitoring of Cloudflares global SSL certificates which often contain large blocks of domains.
- Both 1, and 2.
The next issue was how they would go about registering domains so quickly to other accounts. However, it seems that perhaps the Cloudflare API is being misused here. I "think" that the network could be taking the list of above domains and using the Cloudflare API to see if they "add" the site to an account controlled by the network. A brute force method, if you will, of catching domains that have been removed but were once hosted by Cloudflare, and might still be pointed such as mine was.
RESOLUTION
Cloudflare closed the issue on the grounds that owners of the domain can simply re-point there domain to resolve the issue.
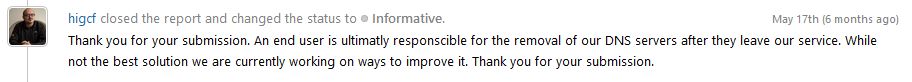
While this absolutely true. It does not resolve the fact that Cloudflare API is being misused, or that once a domain is hi-jacked it can't be re-added to Cloudflare by it's real owner. This is still true today 6 months after the original report.
While i can't presume to understand the limitations in a system as expansive as Cloudflare provides the world. I strongly urge Cloudflare to upgrade there system by adding unique TXT record validation of domains that are added.
